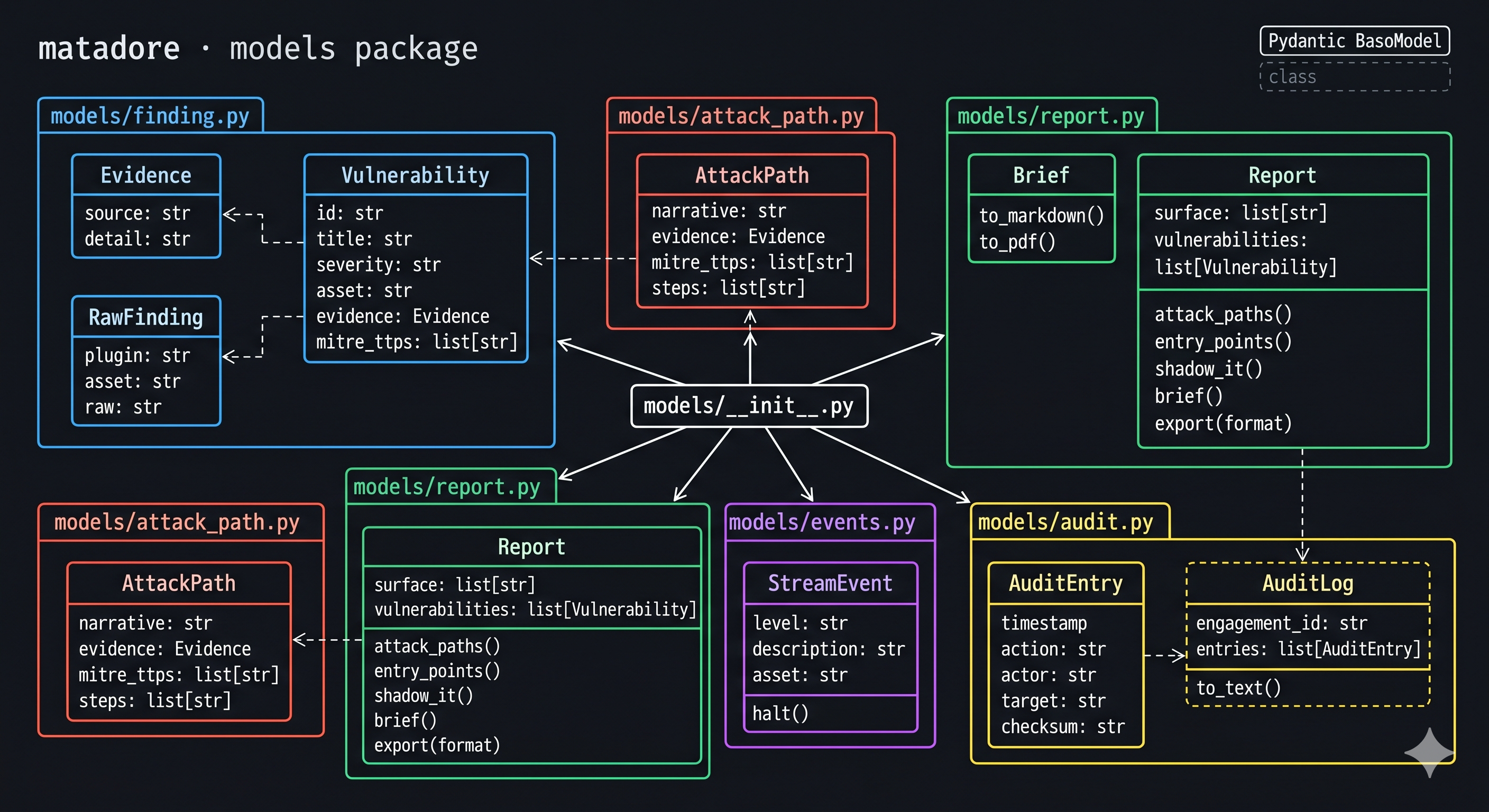
Domain Models¶
Matadore's data layer is built entirely on Pydantic v2 models.
Every finding, attack path, and report object is fully typed and validated - the AI cannot
assert a claim without a verifiable Evidence reference.
Package layout¶
src/matadore/models/
├── finding.py # Evidence, RawFinding, Vulnerability
├── attack_path.py # AttackPath
├── report.py # Report, Brief
├── events.py # StreamEvent
└── audit.py # AuditEntry, AuditLog
All models are re-exported from matadore.models so you can import from either location:
Models¶
Pydantic models for individual security findings.
Every :class:Vulnerability carries a mandatory :class:Evidence field -
the AI cannot assert a finding without a verifiable source reference (port
response, code line, API payload, etc.).
Evidence
¶
Bases: BaseModel
Verifiable source reference for a finding.
Attributes:
| Name | Type | Description |
|---|---|---|
source |
str
|
Where the evidence came from (e.g. |
detail |
str
|
The raw data that substantiates the finding (packet capture excerpt, code snippet, API response body, etc.). |
Source code in src/matadore/models/finding.py
RawFinding
¶
Bases: BaseModel
Unprocessed output from a scanner plugin before LLM reasoning.
Attributes:
| Name | Type | Description |
|---|---|---|
plugin |
str
|
Name of the plugin that produced this finding. |
asset |
str
|
The target asset (IP, URL, repo path, etc.). |
raw |
str
|
Raw output string from the underlying tool. |
Source code in src/matadore/models/finding.py
Vulnerability
¶
Bases: BaseModel
A single security finding with mandatory evidence.
Attributes:
| Name | Type | Description |
|---|---|---|
id |
str
|
Unique finding identifier, e.g. |
title |
str
|
Short human-readable description. |
severity |
str
|
|
asset |
str
|
The target asset this vulnerability was found on. |
evidence |
Evidence
|
Verifiable source reference - never empty. |
mitre_ttps |
list[str]
|
ATT&CK technique IDs applicable to this finding. |
Source code in src/matadore/models/finding.py
Pydantic model for chained exploit sequences (kill chains).
AttackPath
¶
Bases: BaseModel
A chained exploit sequence from initial access to impact.
Attributes:
| Name | Type | Description |
|---|---|---|
narrative |
str
|
Human-readable kill chain description. |
evidence |
Evidence
|
Source data that substantiates every step in the chain. |
mitre_ttps |
list[str]
|
Ordered ATT&CK technique IDs for each hop. |
steps |
list[str]
|
Ordered list of asset/action pairs describing the path. |
Source code in src/matadore/models/attack_path.py
Report and Brief models returned by an engagement.
Brief
¶
Narrative red team report generated from a :class:Report.
Source code in src/matadore/models/report.py
to_markdown()
¶
Report
¶
Full engagement report returned by :meth:~matadore.Matadore.engage.
Attributes:
| Name | Type | Description |
|---|---|---|
surface |
list[str]
|
All exposed assets discovered during the engagement. |
vulnerabilities |
list[Vulnerability]
|
Findings ranked by exploitability, with evidence. |
_audit |
Internal audit log for this engagement. |
Source code in src/matadore/models/report.py
assert_no_new_criticals()
¶
Raise if new critical findings were discovered.
Use as a CI/CD gate::
report.assert_no_new_criticals()
attack_paths()
¶
audit_log()
¶
brief()
¶
delta(previous)
¶
entry_points()
¶
export(format, path=None)
¶
Export the report to format.
Parameters:
| Name | Type | Description | Default |
|---|---|---|---|
format
|
str
|
|
required |
path
|
str | None
|
Optional file path to write the output to. |
None
|
Returns:
| Type | Description |
|---|---|
str
|
The exported content as a string (SARIF JSON, Markdown, etc.). |
Source code in src/matadore/models/report.py
mitre_mapping()
¶
remediation_plan()
¶
shadow_it()
¶
summary()
¶
Models for real-time streaming events emitted during an engagement.
StreamEvent
¶
Bases: BaseModel
A single finding or status event emitted during stream=True mode.
Attributes:
| Name | Type | Description |
|---|---|---|
level |
str
|
Severity label - |
description |
str
|
Human-readable description of what was found or observed. |
asset |
str
|
The asset that triggered this event (URL, IP, file path, etc.). |
_halt_fn |
Callable[[], None] | None
|
Internal callable to stop the engagement early. |
Source code in src/matadore/models/events.py
halt()
¶
Stop the running engagement immediately.
Safe to call from inside a for event in m.engage(..., stream=True)
loop - the generator will stop after this event is yielded.
Source code in src/matadore/models/events.py
Audit log models for tamper-evident chain of custody.
AuditEntry
¶
Bases: BaseModel
A single immutable record in the engagement audit trail.
Attributes:
| Name | Type | Description |
|---|---|---|
timestamp |
datetime
|
UTC timestamp of the event. |
action |
str
|
Short action label (e.g. |
actor |
str
|
Who or what performed the action (plugin name, |
target |
str
|
The asset or resource the action was performed against. |
detail |
str
|
Free-form detail string for human review. |
checksum |
str
|
SHA-256 of the entry fields for tamper detection. |
Source code in src/matadore/models/audit.py
AuditLog
¶
Bases: BaseModel
Ordered, tamper-evident chain of custody for an engagement.
Attributes:
| Name | Type | Description |
|---|---|---|
engagement_id |
str
|
Unique identifier for this engagement run. |
entries |
list[AuditEntry]
|
Ordered list of audit entries. |
Source code in src/matadore/models/audit.py
append(entry)
¶
to_text()
¶
Return a human-readable audit trail.